iOS
AdGuard Home & Tailscale for maximal DNS privacy
DNS is a privacy minefield. Here's my best shot at charting a safe course through.

Regardless who you are, what devices you use, or how you connect to the internet, you use a domain name server (DNS) resolver. You may not know who your DNS resolver is, in which case your DNS and Internet Service Provider (ISP) are likely one-and-the-same, or you may at some point have set your device to use a third-party alternative, like 1.1.1.1 (Cloudflare) or 8.8.8.8 (Google). Regardless, if you're reading this, there's a strong likelihood that your DNS resolver knows who you are. Worse, your DNS resolver likely knows what you do—i.e., every site you visit. And it probably does stuff with that knowledge.
The good news? You can (and should) choose your DNS resolver(s). Heck, you can even be your own DNS resolver. Read on to learn why you might not want to go quite that far, and how I, for one, navigated the DNS privacy minefield.
Why start here?
When I launched this blog two months ago, I had a couple dozen ideas for topics to post about, and while this was one of them, it didn't top my list. But after two months running through the options and the reasons each might be the best starting point, I realized the obvious: it's more important to just start somewhere. And, at least as far as privacy is concerned, the subject of DNS may actually be a great place to start. After all, explaining my decision to build my own Linux server, or rely on Tailscale for connections between all my devices—both subjects of future posts—could ring a bit hollow without a shared understanding of DNS and the possibilities and vulnerabilities associated with it.
So... what is DNS?
DNS, in a nutshell, is the mechanism that ties each human-comprehensible domain (like sij.law) to a numeric IP address. Numeric IP addresses, in turn, are used to send and request content between your browser and a web server — like when you loaded this post, for instance.
It's helpful to think of DNS resolution as a rather tedious Q&A. When you try to load a page, like https://sij.law/dns, your browser asks your DNS resolver, "What's the IP address for sij.law?" Assuming no one else recently asked that same question (then it answers from memory), your DNS resolver starts a process something like this:
- Your DNS resolver queries one of the 13 root DNS servers—operated by various universities, U.S. and international agencies, and both nonprofit and for-profit corporations—"Who knows about
.lawdomains?" - The root server responds, "Ask the .law TLD servers at
a.nic.lawthroughz.nic.law." (TLD stands for Top-Level Domain) - Your DNS resolver then asks a .law TLD server, "Who knows about
sij.lawspecifically?" - The .law TLD server responds, "Ask Cloudflare's authoritative nameservers for
sij.lawatanuj.ns.cloudflare.comoringrid.ns.cloudflare.com." - Finally, your DNS resolver asks one of Cloudflare's authoritative nameservers, "What are the IP addresses for
sij.law?" - Cloudflare's authoritative nameserver responds with "
172.67.165.115and104.21.57.184" (which incidentally also belong to Cloudflare, because my site uses Cloudflare proxies for security).
Your DNS resolver then passes these IP addresses back to your browser.
... and? So what?
THE PROBLEM
DNS resolution works by you telling a resolver every time you want to load a site. Once your DNS resolver has done its job—translated a domain into an IP address that your browser can use to load content—you may just as soon be on your merry way to another page, forgetting all about how you got there. But your DNS resolver most certainly has not forgotten. Your DNS resolver probably keeps info about your browsing habits. And you really have no idea what it does with that information.
Are you... okay with that!?
I'm not. So I researched and trialed a number of options in my quest for genuine DNS privacy. Here are the options I considered, and why I didn't accept them as good enough.
Privacy-oriented DNS resolvers
I began my quest for the ultimate DNS privacy solution in an obvious place: privacy-oriented DNS resolvers. This category includes Quad9 — 9.9.9.9 and 149.112.112.112 (traditional DNS servers usually come in sets of two IP addresses for redundancy in case the first fails) — and Mullvad -- 194.242.2.2 and 2a07:e340::2 (the funky-looking second one is an IPv6 address, which is beyond the scope of this post, or—if we're being honest—any likely future post), among numerous others.
What sets these DNS resolvers apart from, say, Google, are generally good privacy policies (e.g. not keeping logs), backed by strong respective reputations in privacy and information security ("infosec") spaces. The reason I decided to look further, beyond simply punching in Quad9's or Mullvad's IPs in my systems' DNS settings, was two-fold:
First, DNS queries are typically made in unencrypted, plain-text form over port 53 to the DNS resolver. This means my ISP, and anyone else in a position to monitor my web traffic, can readily identify the sites I visit. For me, this was unacceptable.
Second, I adhere as faithfully as I can to a 'zero trust' approach to infosec, which can be summarized as "never trust, always verify." In practice this means configuring and exclusively using systems that don't depend on the trustworthiness of anyone besides myself and my closest / most trusted associates. Obviously, zero trust is often more aspirational than actually possible in absolute terms. But even if using the internet necessarily involves placing some degree of trust in others, I have deep qualms about trusting profit-driven companies to abide their privacy policies—especially when it comes to information as deeply personal as my complete browsing history. Quad9 and Mullvad both profess not to keep any logs of DNS queries, but users ultimately have to take them at their word. Nothing actually prevents them from keeping logs tying specific domains to specific users. For that matter, nothing inherently prevents resolvers like Quad9 and Mullvad from complying with requests from government actors to surveil users, independent of whether they themselves "keep" logs. For me, this too was unacceptable.
DNS-over-HTTPS, DNS-over-TLS
The obvious answer to the problem of all DNS queries being exposed to one's ISP (or eavesdroppers) is to use encrypted DNS, i.e., configuring one's devices to use DNS-over-HTTPS (DoH) or DNS-over-TLS (DoT).
Most operating systems—at least those with which I am most familiar (macOS, iOS, Debian Linux)—do not natively support DoH or DoT, but it's rather straightforward using third-party software I'll mention at the end.
While this approach prevents an ISP directly monitoring which sites you visit, it does not solve the distinct problem of having to trust your DNS resolver. They'll still know (a) who you are, and (b) what sites you visit.
Pi-hole & Unbound for self-hosted recursive DNS resolution?
Once I got this far into the murky depths of DNS, I encountered repeat mentions of a "pie hole". Turns out they meant Pi-hole. It's free open-source ("FOSS" henceforth) DNS software that's actively developed by a large community of developers. Turns out Pi-hole is pretty great at a lot of things, like network-wide ad- or content-blocking with user-specific rulesets, and—more relevant here—acting as one's own recursive caching DNS resolver by pairing it with Unbound (also FOSS).
"What the ƒ#@% is a recursive caching DNS resolver!?" I hear you ask?
Recall the tedious Q&A we outlined. A recursive caching DNS resolver, like Pi-hole with Unbound, performs this entire Q&A process itself, starting from the root and working its way down. It then remembers the answer for a while, so it can respond more quickly to future questions about sij.law without having to ask everyone all over again.
This approach has significant pros & cons:
- Pros: you're not relying on any third-party DNS resolver. You're querying the authoritative sources directly and caching the results yourself. This eliminates the privacy concerns associated with trusting one DNS resolver with all your queries. You're also positioned to implement industrial strength ad-blocking or web-filtering rules for your entire network.
- Cons: authoritative DNS servers do not accept encrypted DNS queries. Let me repeat that, because too often this caveat isn't acknowledged in DNS privacy discourse that seems to favor Pi-hole + Unbound. Authoritative DNS servers. DO. NOT. ACCEPT. encrypted DNS queries. All DNS queries to authoritative DNS servers are made in UNENCRYPTED, PLAIN-TEXT form. This puts us back to square one with our ISP (and anyone else listening in) able to easily monitor every site we visit.
The astute reader will now ask: if all DNS queries are ultimately decrypted and sent over the open internet to authoritative DNS servers in plain text anyway, what's the point of encrypted DNS anyway? What's the point of any of this?
Well, the problem with being your own recursive caching DNS resolver is that all DNS queries you make are presumptively your own. Your ISP knows, the authoritative DNS servers knows, and anyone else listening in also knows—they know it's you.
By contrast, when you use a DNS resolver like Mullvad or Quad9 over encrypted DNS, your ISP doesn't know what you're doing, and while the DNS resolver's ISP and the authoritative DNS can see you what you're doing, they don't know who you are. All they see is a firehose of undifferentiated DNS queries going through a major DNS resolver, each presumptively from anyone anywhere in the world.

Think of it like digital black bloc—anonymity in a faceless crowd.
But as we already discussed, that approach entails a critical vulnerability: placing trust in a single DNS resolver (to strain the metaphor a tad: the black bloc clothing shop), which does know both (1) who you are, and (2) what you are doing.
A SOLUTION
By now, it became evident to me that there's no such thing as absolute DNS privacy and anonymity. The best you can do is:
- Conceal what you are doing from anyone that knows who you are,
- Conceal who you are from anyone that knows what you are doing, and
- Conceal the fact that your DNS queries all come from one source, even if that source is anonymous per #2.
I knew all three measures are independently possible, so the challenge became to achieve them together. Cue—
AdGuard Home
AdGuard Home, like Pi-hole, is FOSS you can install on a small at-home server (think Raspberry Pi, old MacBook, or Intel NUC), or a cheap Virtual Private Server (VPS), which handles DNS for your entire network. Like Pi-hole, it offers network-wide ad-blocking and custom filtering rules. But AdGuard Home comes with key DNS privacy functionality that Pi-hole doesn't:
- Built-in support for DNSCrypt: AdGuard Home natively supports DNSCrypt between itself and the upstream DNS server(s). This ensures your DNS queries are encrypted all the way to your upstream servers, concealing what you're doing from your AdGuard Home's ISP (which will typically know who you are) while also ensuring your upstream servers are who they purport to be—not imposters.
- Multiple upstream resolvers: AdGuard Home allows you to enter a list of upstream DNS resolvers and will rotate through them all, dividing your queries between multiple servers in multiple jurisdictions. This prevents any single resolver/authority building a complete profile of what you do, which could be used to infer with substantial certainty who you are.
- Built-in support for DoH and DoT: AdGuard Home natively supports DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) between your devices and AdGuard Home. These encryption protocols conceal what you are doing from your devices' ISPs and any other eavesdroppers between your devices that already know who you are.
Of course, without more, individual upstream DNS servers you select still know who you are. That brings us to—
Tailscale
Tailscale is an incredibly useful tool that essentially creates a virtual private network (VPN) between your devices, allowing you to access services on any one from any other, anywhere in the world.
Tailscale is free for personal use on up to 100 devices (more than most households will ever need), and offers extremely competitive pricing for business use.
Tailscale offers three key functionalities relevant here:
- Tailscale secures all traffic between your devices using the ironclad
wireguardend-to-end-encryption (E2EE) protocol. This is a privacy boon for any number of use cases, but most relevant here, it ensures DNS queries from any devices that can't natively configure DoH or DoT are nevertheless encrypted from that device to your AdGuard Home server. - Tailscale allows you to force your devices to all use the DNS service you specify. While some router's firmware lets you direct all DNS queries to a particular server over DoH or DoT, (a) not all do, and (b) you likely access the internet from a mobile device from time-to-time over other networks where your router isn't relevant. When you put your AdGuard Home server on the same Tailscale network ('tailnet') as your devices, you allow those devices to rely on AdGuard Home for DNS queries from anywhere in the world.
- Tailscale has a partnership with Mullvad to add privacy VPN functionality to any tailnet. You've likely heard of privacy VPNs—other noteworthy options include ProtonVPN, NordVPN, and WindScribe. What these all have in common is they will route your internet traffic over an encrypted tunnel to an 'exit node' somewhere in the world, concealing who you are from the sites you visit—and anyone else who can see what you are doing. Privacy VPNs aren't typically free, and the Mullvad extension for Tailscale is no exception. But at $5/mo for up to 5 devices, it's very competitively priced.
SETTING IT UP
- Choose a server for AdGuard Home
You can run AdGuard Home on macOS, Windows, Linux, or more specialized OSs like Raspberry Pi or TrueNAS SCALE. It doesn't matter much which device or operating system you choose, except that it should be 'high availability'—online and accessible 24/7—if you intend to use it for DNS resolution on other devices. You could install it on your laptop and use it effectively on that laptop, but your smartphone couldn't use it when your laptop is out of juice or asleep in a bag.
In future posts I'll discuss my home servers and the dedicated Debian server I rent at a Finnish datacenter. Without going into the specifics of selecting or building one just yet, I do recommend using a server for AdGuard Home. Servers are typically higher availability than end user computers, making them more suitable for multi-device setups.

Finally, if you intend to enable DoH, I recommend running AdGuard Home on the same server as Caddy so it can share access to the HTTPS certificates that Caddy automatically renews.
- Install and configure Tailscale on the server (and the device you're using to access it, if separate).
Tailscale is straightforward to setup, but first you'll need an account. A free one will work, but please make sure you're in compliance with Tailscale's policies for free vs. business accounts.
Once you've created a Tailscale account, install Tailscale on the same server that will run AdGuard Home, and if it's not the computer you're using to access it, install Tailscale on the local device too.
You can snag Tailscale on the macOS and iOS app stores. For Linux servers including Debian, Tailscale has wizard for creating an installation script. Windows and Android users are on their own (fair warning: my readers will see this a lot), but I suspect it's similarly straightforward to install there too.
Take note of your server's Tailscale IP address—it'll begin with 100.
100.64.64, with routers occupying the .1–9 range, servers occupying the .10–.19 range, my own devices occupying the .20–.49 range, and family members' devices occupying the .50–.99 range. This makes it easier to remember the IPs of specific devices and to know what type of device an IP belongs to even if I don't immediately recall which specific device it is.- Install AdGuard Home
The steps for installing AdGuard Home will depend on the device you're using, so please see the official documentation for other device-specific instructions. To install AdGuard Home on Debian:
curl -s -S -L https://raw.githubusercontent.com/AdguardTeam/AdGuardHome/master/scripts/install.sh | sudo sh -s -- -v
sudo /opt/AdGuardHome/AdGuardHome -s startStandard method for installing and starting AdGuard Home on Linux
- Initial AdGuard Home configuration
Open a new browser tab, navigate to http://Your-Tailscale-IP:3000, and begin the initial 5-step configuration.
On the second step, I recommend setting the listen interface for both the Admin Web Interface and the DNS Server to your Tailscale IP address, to ensure only devices you've added and authorized on Tailscale can access it directly. You'll also need to select a different port than the default of 80 if you intend to run Caddy on the same server (as I recommend if you're looking to configure DoH), or if you're running another reverse proxy or web server. I've adopted port 8052 for this purpose.
Be sure to create a very secure password on the third step.
Once you've completed the initial configuration, visit http://Your-Tailscale-IP:Admin-Web-Interface-Port. For me, for example, that is http://100.64.64.11:8052. Login with the credentials you just created.
- Add upstream DNS resolvers to AdGuard Home
You should now be greeted by the AdGuard Home admin panel. Click Settings > DNS settings, and you should see a field for entering a list of Upstream DNS servers. I recommend finding upstream DNS resolvers to use on DNSCrypt.info, or directly from this GitHub file.
I won't share my upstream resolvers because that would somewhat defeat my own DNS privacy, but I can share some tips for choosing your upstream resolvers:
- Choose servers that support DNSCrypt and DNSSEC to ensure your DNS queries aren't tampered with.
- Choose servers that profess not to keep logs.
- Avoid servers that apply ad-blocking or filtering rules. If you want this functionality it's best to set it up yourself within AdGuard Home rather than relying on rules set on an upstream server outside your control.
- Choose a healthy mix of servers around the world, but especially in your region to ensure fast DNS responses.
- Choose a few servers from established privacy or infosec companies like Mullvad, Njalla, and Quad9. These will typically have the infrastructure to fulfill your DNS requests quickly and strong privacy policies, and are less likely to become defunct (which many servers listed on DNSCrypt.info seem to).
- Rely on the
sdns://DNS stamp method of adding servers. These "stamps" encode all the information needed to connect to a DNS server, much like QR codes, streamlining the process. - Add a comment above each server in your list so you remember what/where it is.
- Aim for around a dozen servers. The more you have, the smaller the proportion of your total DNS queries any one server will have, boosting your DNS privacy. On the other hand, the more you have, the more likely you are to select one that becomes defunct.
- Scroll down and click
Test upstreamsafter adding each server, so you immediately know if it's defunct. Replace the last server you added if the test ever fails.
- Configure the remaining DNS settings on AdGuard Home
Once you've added a dozen or so upstream DNS resolvers that test successfully, there are a few more settings on the same page (DNS Settings):
- Select
Load-balancing. - Add one or more
Fallback DNS servers. You can get these from the same list as the primary upstream DNS servers discussed above, and use the same syntax (including the recommendedsdns://DNS stamp method). I recommend using established DNS privacy providers like Mullvad, Njalla, or Quad9 here. - Add one or more
Bootstrap DNS servers. Here you need to enter traditional IP addresses. I use Quad9 and Mullvad for this, so I've entered9.9.9.9,149.112.112.112, and149.112.112.10. - Again
Test upstreamsto ensure everything here is copacetic. - Scroll further down and
Enable EDNS client subnet. - For privacy reasons (which is why we're here after all), you should also
Use custom IP for EDNS. The IP you enter here may affect how quickly your DNS queries are answered, so it's a good idea to select the IP of an institution near you—e.g. a university, library, or hospital. For example, if you live in Michigan, you could rundig umich.eduand enter the resulting IP address. Enable DNSSEC.- Set the
Cache sizeto a higher value, e.g., 67108864 bytes (64 megabytes). - Enable
Optimistic caching. This will result in fewer DNS queries reaching your upstream servers, enhancing your privacy and speeding up DNS resolution—possibly dramatically. The drawback—the occasional invalid DNS response the first time after a site's DNS has changed (rare)—is well worth the benefit. - Under
Allowed clients, enter127.0.0.1, and the narrowest CIDR range that encompasses all your Tailscale IPs. For me, that's100.64.64.0/24.
- Configure Tailscale to enforce AdGuard Home as the only DNS for your tailnet
Return to the Tailscale admin console and navigate to the DNS tab. Scroll down to Nameservers and remove any that may be listed under Global nameservers.
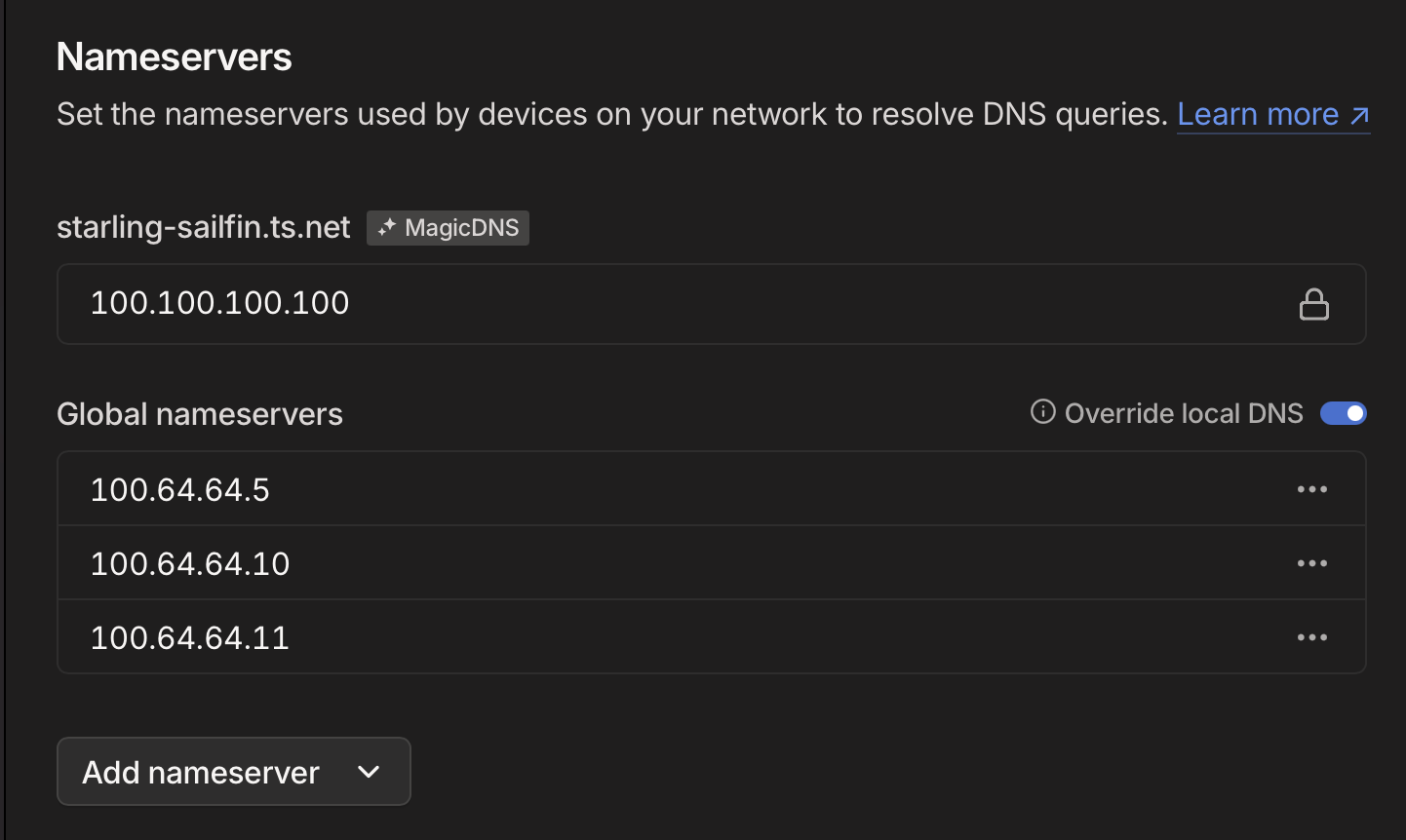
Here, add the Tailscale IP address of your AdGuard Home server, and enable Override local DNS.
- Semi-Optional: Enable Mullvad on your AdGuard Home server
Still on the Tailscale admin console, navigate to the Settings tab, find the section for Mullvad VPN, and click Configure. Purchase the add-on for $5/month, then add the AdGuard Home server to the list of devices authorized to use Mullvad exit nodes.
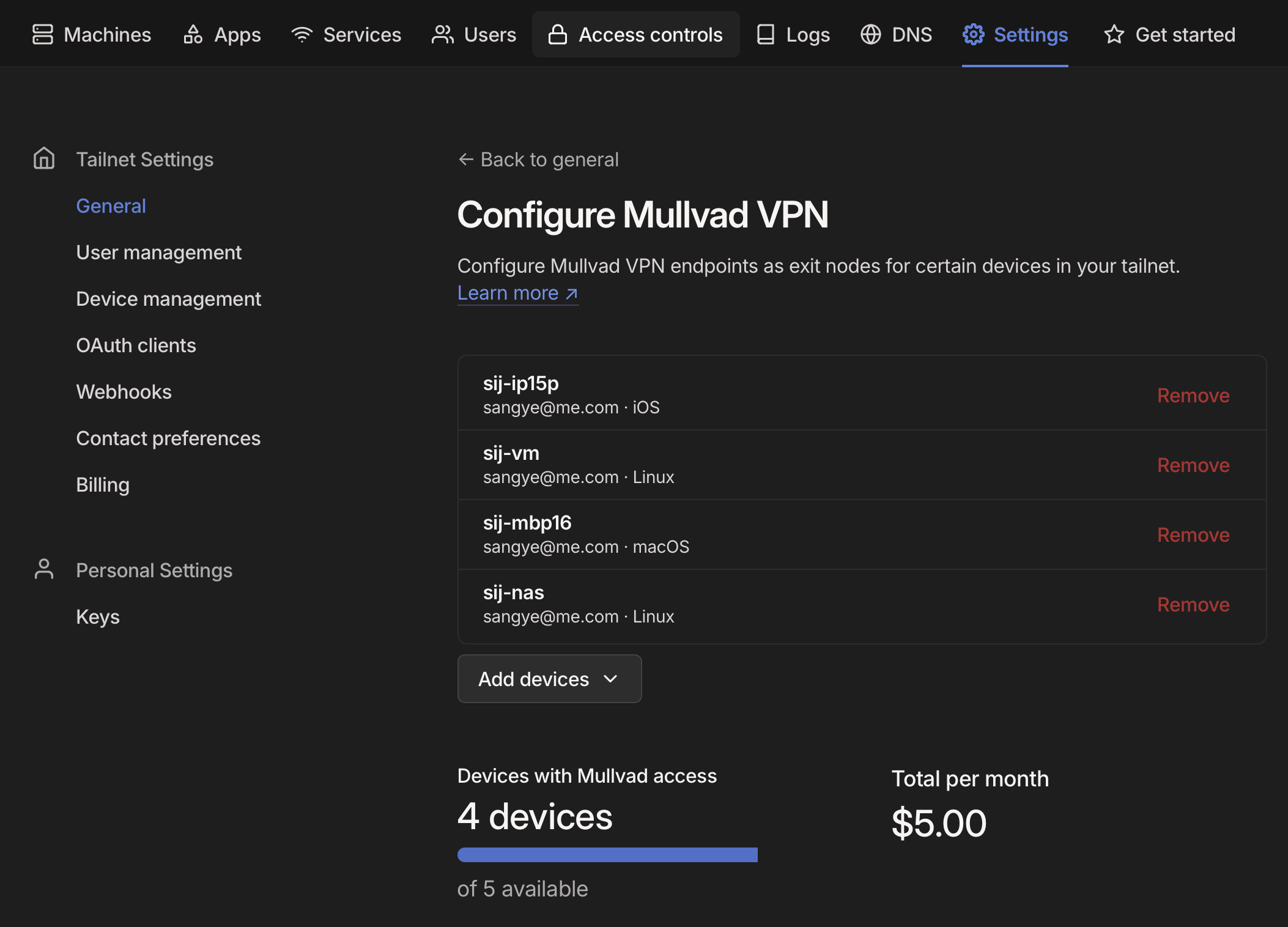
On your AdGuard Home server, set Tailscale to connect to a Mullvad exit node. On Debian: tailscale exit-node list; find one in a privacy-friendly jurisdiction like Switzerland, Sweden, or Finland; then tailscale set --exit-node-allow-lan-access --accept-dns=true --exit-node=Hostname-or-IP-address-of-Mullvad-exit-node.
- Optional: Set up blocklists for ads, malware, etc.
If you've gotten this far, AdGuard Home is uniquely well positioned to block ads across your entire network—before they ever reach your browsers' own ad-blocker. It's why this powerful multi-purpose software is called 'AdGuard', after all. If you want to take advantage of this core functionality—which you absolutely should—navigate to Filters -> DNS Blocklists -> Add blocklist.
Here you can either choose from a great assortment of blocklists that come with AdGuard Home by default, or add your own. I've not tested the options extensively, but have had good results enabling the following:
- AdGuard DNS Filter
- AdAway Default Blocklist
- Malicious URL Blocklist (URLHaus)
- Dan Pollock's List
- 1Hosts (Lite)
- Dandelion Sprout's Anti-Malware List
- Steven Black's List
- HaGeZi's Pro Blocklist
- OISD Blocklist Small
- Peter Lowe's Blocklist
- Optional: Set up a DNS rewrite rule to easily tell if you're using AdGuard Home
DNS hijacking is a thing, and while the methods detailed here (in particular Tailscale and DNSSEC) should prevent that occurring, you can easily set up a simple DNS rewrite rule that will prove you're using AdGuard Home and not an imposter, for your continued peace of mind.
On the AdGuard Home admin panel, navigate to Filters -> DNS Rewrites -> Add DNS Rewrite, enter a made-up domain like adguard.dns.rewrite, and point it to your Caddy IP address or to another domain. Then, when you visit http://adguard.dns.rewrite, you'll know you're using AdGuard Home if your browser takes you to the location you've configured.
- Optional: Set up DoH and configure Caddy
The instructions I'll provide here may not be compatible with Mullvad exit nodes depending on your setup. It works for me, but this configuration is stretching the limits of my know-how (I know just enough to know things could get squirrelly here depending on firewall rules, Tailscale ACLs, etc). If a reader can provide a more confident explanation of this setup, that would be lovely.
This step has some prerequisites that I might cover in a future post but for now are beyond the scope:
- You need to have installed Caddy on the same server as AdGuard Home and configure it to use Cloudflare for HTTPS challenges.
- The server with Caddy and AdGuard home on it needs to have a permanent IP address. You need to own a subdomain (e.g.
dns.sij.law) and assign it to this IP address.
Edit your Caddyfile — typically it's at /etc/caddy/Caddyfile —
sudo nano /etc/caddy/Caddyfile
You will want to make sure your email address is included in it, for HTTPS certificate acquisition. Then add an entry for AdGuard Home.
{
log {
output stdout
format console
level DEBUG
}
admin 127.0.0.1:2019
servers {
metrics
}
# replace with your email address
email [email protected]
acme_ca https://acme.zerossl.com/v2/DV90
}
# replace this with a subdomain you've pointed to your server's public IP address
dns.sij.law {
tls {
dns cloudflare {env.CLOUDFLARE_API_TOKEN}
}
@doh {
path /dns-query
header Accept application/dns-message
}
handle @doh {
reverse_proxy https://localhost:8053 {
transport http {
tls_insecure_skip_verify
}
}
}
handle {
reverse_proxy http://localhost:8052
}
log {
output file /var/log/caddy/dns.sij.law.log
format json
}
}
Your Caddyfile might look something like this.
Save it (Ctrl+O), exit Nano (Ctrl+X), then restart Caddy:
sudo systemctl restart caddy
Navigate back to the AdGuard Home admin panel, then Settings -> Encryption settings:
Enable Encryption (HTTPS, DNS-over-HTTPS, and DNS-over-TLS.- Leave
Enable plain DNSon for standard DNS over Tailscale. - Set
Server nameto the subdomain you added to Caddy. - Do not enable
Redirect to HTTPS automatically. - Set the HTTPS port to
8053and the DNS-over-TLS port to8054. - Under Certificates,
Set a certificates file pathandSet a private key file.You'll need to find where Caddy saved these files on your local filesystem. For me, these file paths are:/var/lib/caddy/.local/share/caddy/certificates/acme.zerossl.com-v2-dv90/dns.sij.law/dns.sij.law.crt/var/lib/caddy/.local/share/caddy/certificates/acme.zerossl.com-v2-dv90/dns.sij.law/dns.sij.law.key
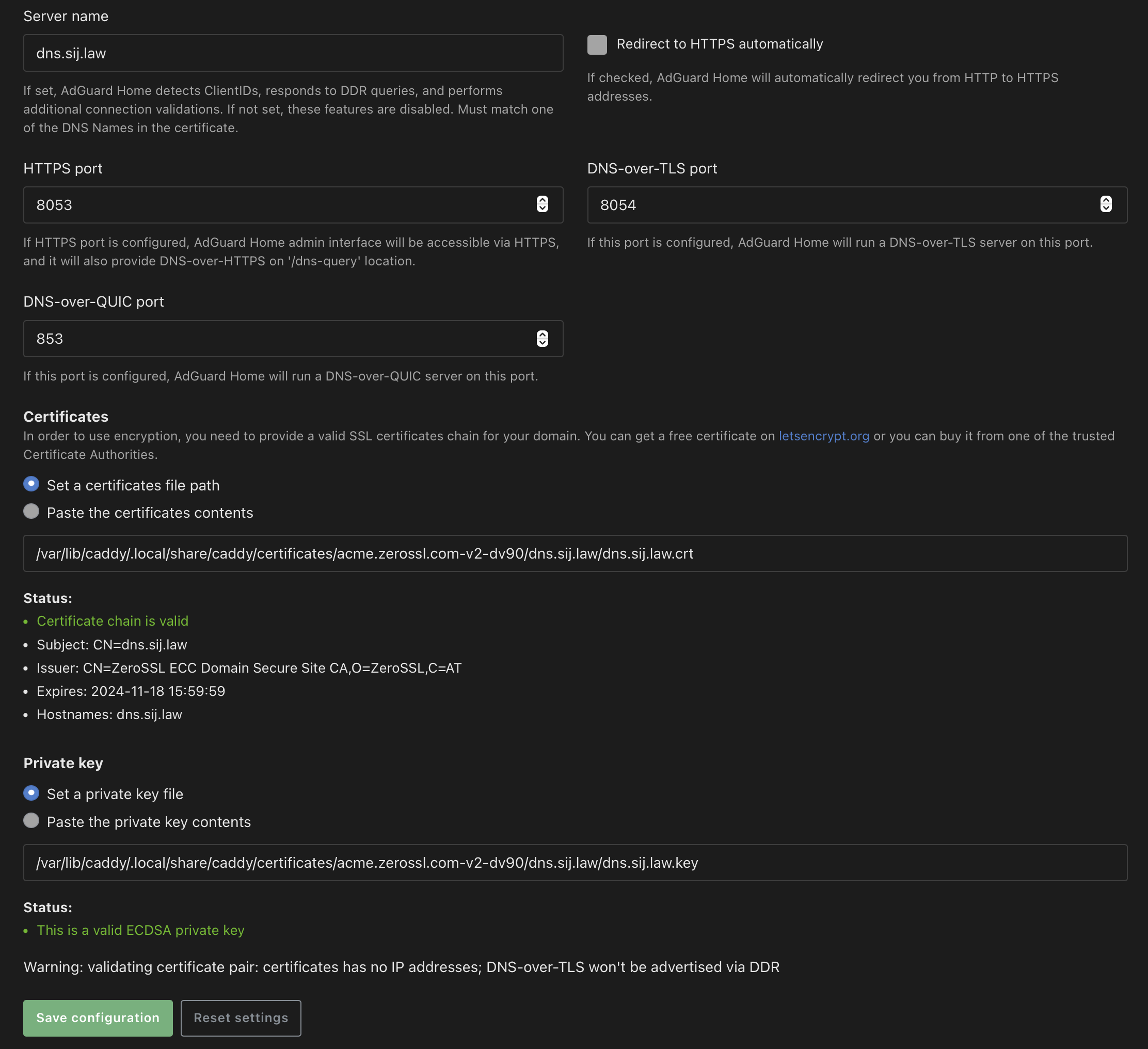
- Once you've entered your certificate and private key file paths, ensure the certificate chain and the private key are recognized as valid.
- Save the settings.
AdGuard Home should now answer DoH requests at the subdomain you configured for it.
Depending on your device's operating system there are various apps and tools you can use to enforce DoH locally. These include:Little Snitch 6 (macOS), DNS Override (iOS and iPadOS).
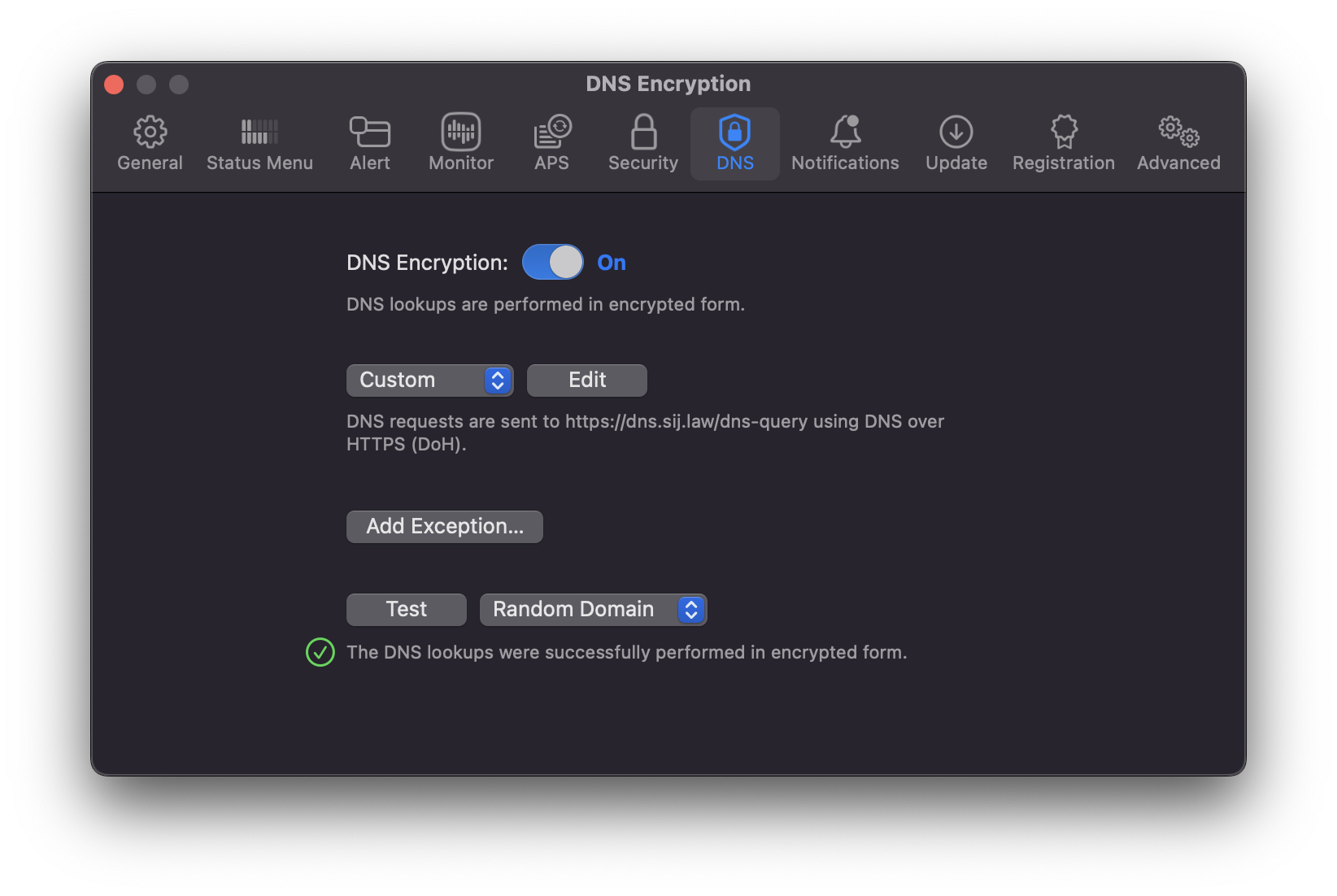
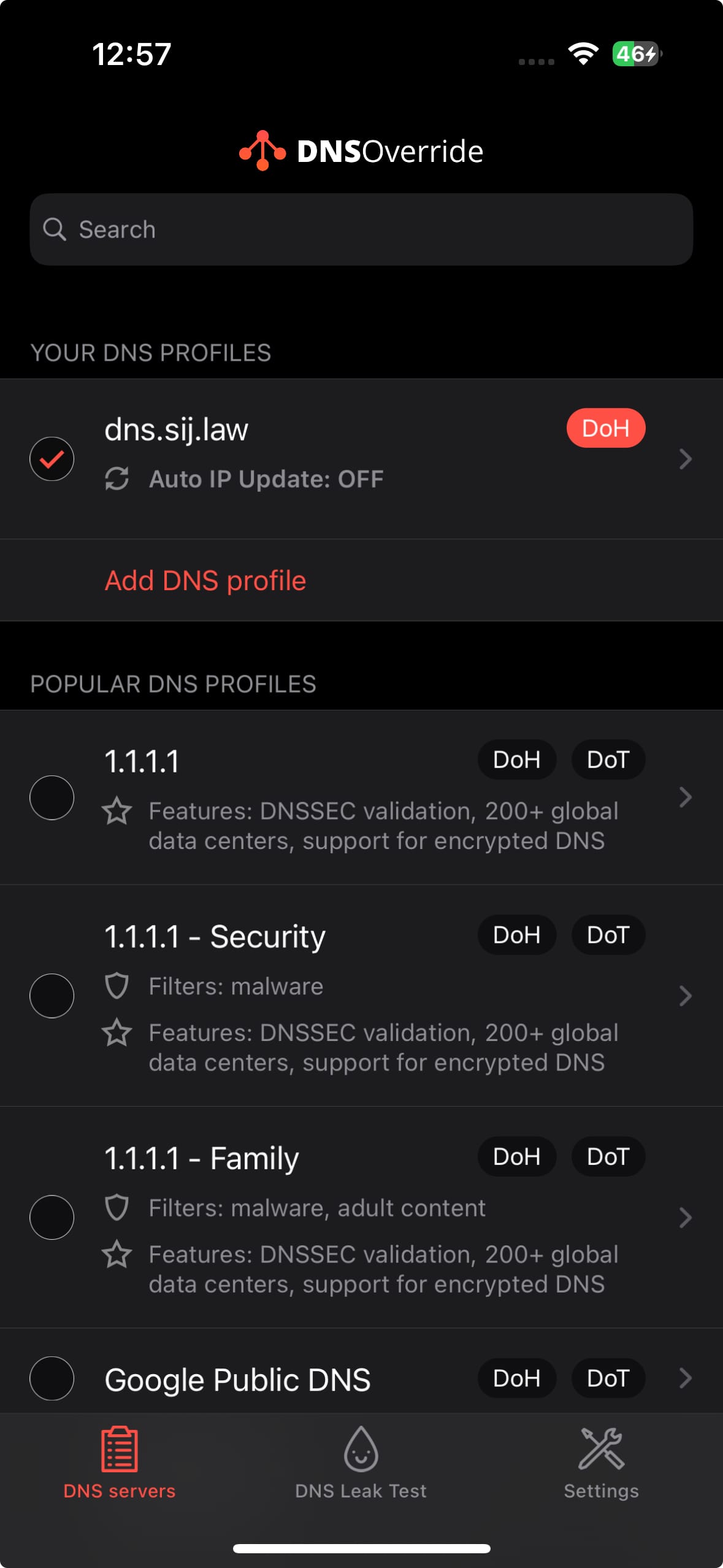
Adding my own DoH server to Little Snitch 6 (macOS) and DNS Override (iOS)
Alright folks, that'll do it for now. Let me know in the comments your approach to DNS privacy, if you're going to try (or already use) something along these lines, and if you'd like to see more privacy-oriented deep dives on this blog.
Cheers,
〄